Skip Certificate Checks with Wget
Category : How-to
This is a reminder for myself more than anything else, on how to get wget to download SSL internet content when it’s encrypted by a self-signed or otherwise unknown certificate.
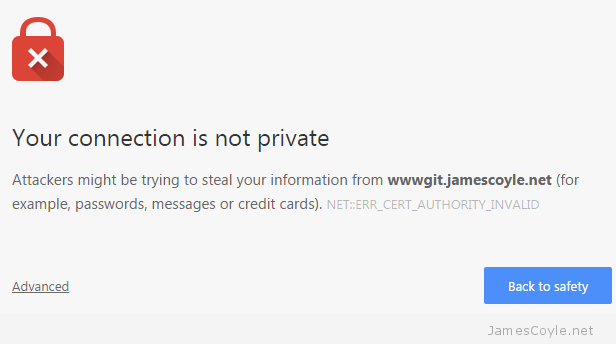
If you haven’t installed or updated your certificate Authority certificates on your computer and try and download something from an SSL URL with wget you’re going to run into trouble because your computer doesn’t know what a valid SSL certificate looks like. You’ll also get a similar problem if the site you’re accessing is encrypted by a self-signed certificate. This example shows a problem downloading from a HTTPS Github URL. Of course, there is no problem with the SSL certificate on Github.com, it’s the local machine that doesn’t have the internets Certificate Authority certificates installed.
Resolving github.com (github.com)... 192.30.253.113 Connecting to github.com (github.com)|192.30.253.113|:443... connected. ERROR: The certificate of 'github.com' is not trusted. ERROR: The certificate of 'github.com' hasn't got a known issuer.
The quickest way round this, albeit not the safest, is to tell wget to ignore any certificate checks and download the file. To do this, add the –no-check-certificate to your wget command. I don’t know why the wget developers couldn’t have chosen a switch that’s easier to remember!
wget https://github.com --no-check-certificate
 As of Zentyal version 4.2 the bundled certificate authority (CA) module is creating signed certificates using the SHA-1 algorithm which is an old algorithm and pretty much deprecated.
As of Zentyal version 4.2 the bundled certificate authority (CA) module is creating signed certificates using the SHA-1 algorithm which is an old algorithm and pretty much deprecated. It’s never been easier to set up your own Git server to host your own git repositories for your projects. Thanks to people like the folks over at
It’s never been easier to set up your own Git server to host your own git repositories for your projects. Thanks to people like the folks over at