OpenVZ containers, or CT for short, work on the premise of using a template as the starting point for each virtual instance. The Template usually holds the basic applications, such as an SSH server, to create a functioning running instance.
See my blog post on Setting up an OpenVZ server for information on creating an OpenVZ server.
Download an OpenVZ Template
OpenVZ hosts a suite of OpenVZ templates for all common Linux distributions. Before you can create a CT you will need to choose a template from the below site and download it to your OpenVZ server. The template must be saved in your servers template directory, by default this is /vz/template/cache.
Download your templates from: http://wiki.openvz.org/Download/template/precreated
I will use the Debian 7 template for this example.
wget -P /vz/template/cache http://download.openvz.org/template/precreated/debian-7.0-x86_64.tar.gz
Create your first OpenVZ container
Most of the administration tasks for a container, such as creating and destroying a container, use the vzctl command.
Before we create our first container we need to understand the components of the create command. This is an example of a basic create command:
vzctl create 200 --ostemplate debian-7.0-x86_64 --config basic
- 200 is the container ID. This is a unique ID which represents the CT being created. We will use this ID later when we start and stop the machine. You can use virtually any number, but we usually use a three digit number.
- –ostemplate is the template file name which we downloaded in the previous section. This file, with a tar.gz extention, must exist in the template directory of your OpenVZ server. By default, the templates directory is /vz/template/cache.
- –config is what decides how much RAM, disk and other properties the CT will assume. OpenVZ have created some example configurations for us, basic being one of them.
Example:
# vzctl create 200 --ostemplate debian-7.0-x86_64 --config basic
Creating container private area (debian-7.0-x86_64)
Performing postcreate actions
CT configuration saved to /etc/vz/conf/200.conf
Container private area was created
List available OpenVZ containers
Now that we have created a container, we can list the details with vzlist. Running this command will list all turned on containers so we’ll need the -a switch to list the turned off ones as well.
# vzlist -a
CTID NPROC STATUS IP_ADDR HOSTNAME
200 - stopped - -
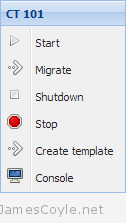
Start/ Stop/ Restart an OpenVZ container
Starting, stopping and restarting a container are done via the vzctl command with either start, stop or restart and the container ID.
vzctl start 200
vzctl stop 200
vzctl restart 200
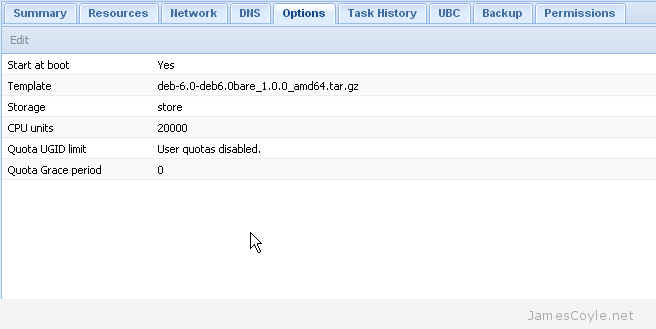
Configure an OpenVZ container
There are many configuration options for an OpenVZ container which specify disk space, SWAP, networking, CPU and plenty of others. I’ll cover a few basic options here.
Networking is a common option, and something we will need in our OpenVZ container. First lets set the hostname to example.jamescoyle.net.
vzctl set 200 --hostname example.jamescoyle.net --save
Next, let’s add an IP address on the same range as our host. Make sure you check that this IP is free and not already in use by another machine on your network.
vzctl set 200 --ipadd 10.10.10.100 --save
The last part of our basic network configuration is to add some nameservers so that DNS entries can be resolved. I’ll use the Google nameservers for this example but you may also wish to include your own local servers.
vzctl set 200 --nameserver 8.8.8.8 --nameserver 8.8.4.4 --save
Execute commands in an OpenVZ container
Using this current example, we can’t connect to our container because we haven’t set a root password. We need to issue the passwd command inside the container and type a password.
There are two ways to do this. We can enter the container directly from the host which will give us a shell running on the container itself.
vzctl enter 200
You can then issue any further commands you require.
The other option is to run a single command from the host using vzctl exec followed by the command to execute.
# vzctl exec 200 passwd
Enter new UNIX password: mypassword
Retype new UNIX password: mypassword
passwd: password updated successfully
Remove an OpenVZ container
Before you remove an OpenVZ container, you must make sure it is stopped. Once the container is stopped, you can use the vzctl destroy command to delete the container permanently.
vzctl destroy 200
Be careful, there is no confirmation for the destroy command!
 OpenVZ servers are hypervisors which allow you to create numerous guest instances within a single hardware node. Unlike other products which offer full hardware virtualisation, OpenVZ creates containers – isolated program execution environments – that share the hardware nodes kernel.
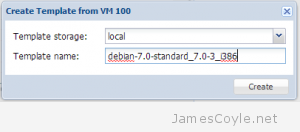
OpenVZ servers are hypervisors which allow you to create numerous guest instances within a single hardware node. Unlike other products which offer full hardware virtualisation, OpenVZ creates containers – isolated program execution environments – that share the hardware nodes kernel. Creating a template from an OpenVZ container is a very manual process. My biggest problem is that you have to have root access to the Proxmox hardware node in order to create a tar from the root of the CT. See
Creating a template from an OpenVZ container is a very manual process. My biggest problem is that you have to have root access to the Proxmox hardware node in order to create a tar from the root of the CT. See